Navigating the Cybersecurity Threat Landscape in the Medical Industry: A 2023 Perspective
August 29, 2023Understanding HIPAA Requirements: The Mandate for Cybersecurity in Physician Practices for 2024
December 12, 2023Cybersecurity breaches in the healthcare sector have become a grim reality, with individual physicians often finding themselves as targets. The cost of a cybersecurity breach goes far beyond financial implications, affecting patient trust, professional reputation, and compliance with legal regulations. This article delves into the multifaceted costs associated with a cyber breach for individual physicians and outlines the crucial steps to take in the aftermath of an incident.
Understanding the Costs of a Cybersecurity Breach
1. Financial Impact: The immediate financial costs of a cybersecurity breach include the expenses of identifying and rectifying the breach, potential ransom payments to regain access to encrypted data, and fines for non-compliance with healthcare regulations like HIPAA. There’s also the long-term financial damage due to lost revenue from downtime and potential litigation costs from affected patients.
2. Loss of Patient Trust: Perhaps the most damaging cost of a cyber breach is the erosion of patient trust. When patients entrust their sensitive health information to their physicians, they expect it to be kept secure. A breach can severely damage this trust, leading to patient attrition and long-term reputational harm.
3. Professional and Legal Repercussions: Physicians may face professional repercussions, including penalties from medical boards and legal consequences for failing to protect patient information. Compliance investigations and audits can further strain resources and focus away from patient care.
Steps to Take Following a Breach
1. Immediate Response: The first step following the detection of a breach is to contain and limit the impact. This may involve disconnecting infected systems from the network to prevent the spread of the breach and engaging cybersecurity professionals to assess and mitigate the damage.
2. Notification: Compliance with laws such as HIPAA requires that affected individuals be notified of the breach in a timely manner. Physicians must also notify relevant authorities and possibly the media, depending on the scale of the breach.
3. Investigation and Remediation: A thorough investigation to understand how the breach occurred is critical. This involves working with cybersecurity experts to analyze the breach’s cause, scope, and exploited vulnerabilities. Subsequently, implementing the necessary remediation measures to prevent future incidents is crucial.
4. Communication: Clear and transparent communication with patients, staff, and partners about the breach, its impacts, and what is being done in response is essential. This can help to restore trust and confidence.
5. Review and Enhance Security Measures: Post-breach, it’s vital to review and strengthen existing cybersecurity measures. This may include updating software, enhancing firewall protections, conducting regular security audits, and providing training to staff on cybersecurity best practices.
Conclusion
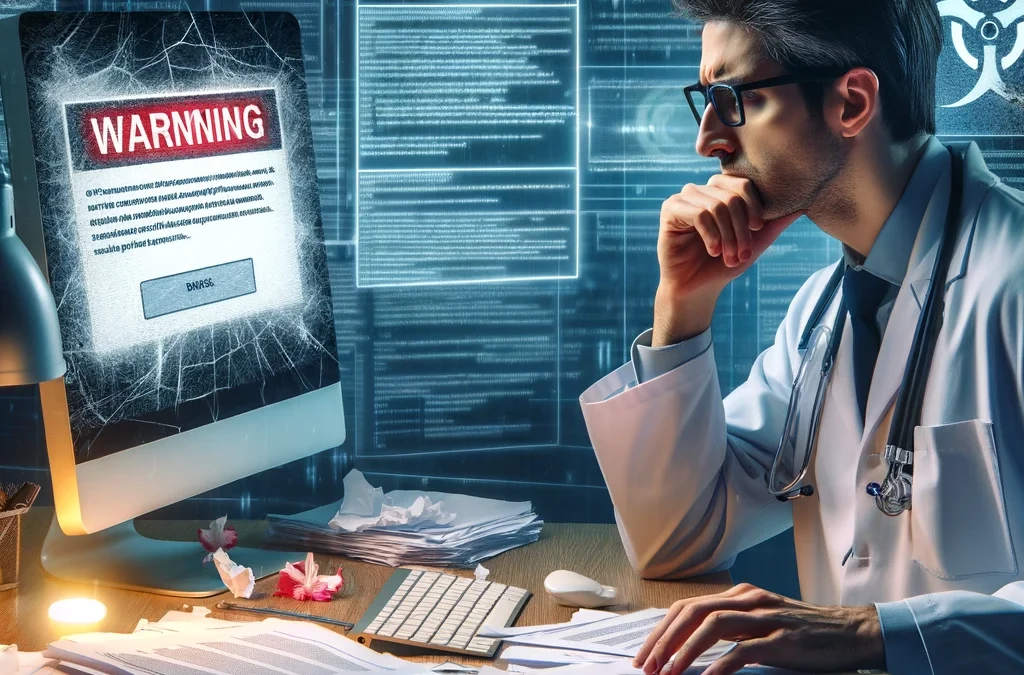
The image accompanying this article captures the chaos and concern following a cybersecurity breach in a physician’s office. It serves as a stark reminder of the serious implications of cyber attacks. For individual physicians, understanding the potential costs and knowing the steps to take following a breach is not just about compliance or financial survival; it’s about maintaining the trust and confidence of their patients. By taking proactive measures to strengthen cybersecurity defenses and having a clear response plan in place, physicians can mitigate the impact of cyber incidents and safeguard their practice’s future.